
DDoS or Distributed Denial of Services attacks is amongst the most perilous attacks that exist on the internet today. It can take a good, smooth-running website down (offline) within seconds. However, the worst part is anyone with a few dollars can launch these attacks.
A mediocre level of DDoS attack can easily shut down huge firewalled websites for hours and even days (if the attack is heavy). Fortunately, there are web hosting tools available that can withhold such attacks and offer safety to the users.
In this article, I will shed comprehensive light on the Distributed Denial of Services (DDoS) and explain how you can survive the DDoS attacks.
“At Value Hosted, one of the biggest concerns that we cater after smooth web optimization is ensuring DDoS protection for customers. These attacks, if not prevented, can ruin websites and hard work of our developers in seconds”
Noitcennok. D, Director (Technical) at Value Hosted
What is a DDoS attack?
To know more about this deadliest attack, we first need to understand its origin; from where the DDoS attacks are derived. For that, we must know a little about Denial of Service (DoS) attacks.

What is Denial of Service (DoS)?
Denial of Service (DoS) is a cyber-attack that overcomes the user’s server or network by sending disrupting, malicious services. Within a few seconds, DoS compromises the network connection until it becomes null on the server (making it completely unavailable).
How does the Denial of Service (DoS) works?
DoS sends multiple service requests at a time that ever server network connection grant access to. Once it is inside the connections, each malicious service then consumes chunks of memory, processing power, and bandwidth.
In simple words, DoS sends malicious network requests that consume the bandwidth and sabotages the entire network, making it disappear from the server.

The perpetrators take advantage of the vulnerability and make numerous connections at a time to send data in bulk that the server or the network cannot withhold. But the question that you might be asking right now is why can’t we just block these service requests?
The answer is you can’t. Because you cannot differentiate between good connections and bad connection as they all look the same to the network resources.
How can I prevent my website or a network from DoS?
The malicious network requests coming from DoS contain an IP address. If we trace the source IP address and block it, the chance of network vulnerability can be less to none. However, the attackers are now well aware of this, which is why they know how to use DDoS attacks (Distributed Denial of Services).
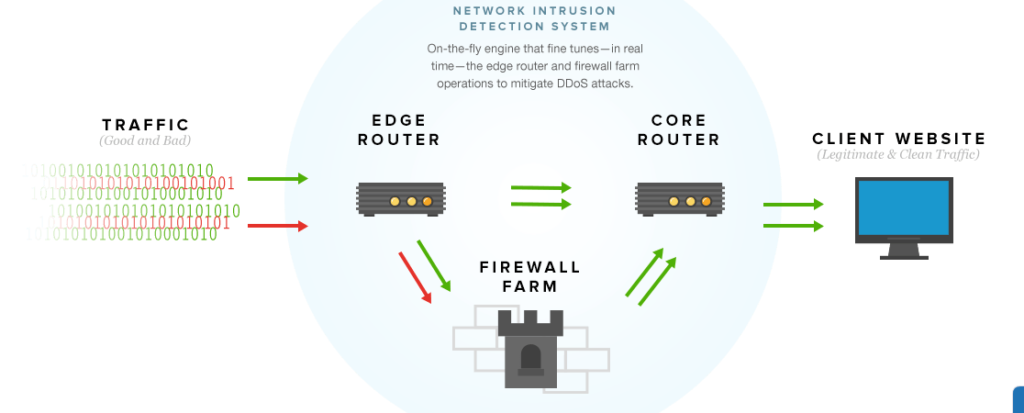
Value Hosted prevent users from these attacks by simply filtering the incoming traffic. The malicious requests that floods the network come using ICMP packets (Internet Control Message Protocol). By using traffic filtration, we block the unwanted packets and the router in parallel separates the clean traffic.

What is a DDoS attack?
Attackers use botnets from compromised servers (mostly available online) to attack the target. In this case, botnets contain thousands of notes that perpetrators can control, instruct remotely to overwhelm all the server resources. Since there are numerous botnets, it becomes difficult to traceroute IP and block them all.
How can I prevent myself from DDoS attacks?
Acquiring a good firewall and configuring it just to stop DDoS attacks is one way. However, a router designated only to prevent these botnets from network infiltration is amongst the best ways to stop DDoS attacks.
Despite this, attackers have found another way to send huge chunks of malicious requests that most firewalls cannot hold (unless you’re a proud Value Hosted customer).
Amplification of DDoS Attacks
When the firewall blocks all the botnets and denies all the network requests, attackers found a way to penetrate it by amplification. Amplification attacks modify the network requests by expecting a much larger response.
Let’s first understand this.
When you visit any website, you send a small amount of data request. In return, the server or the network recognizes the request and responds with much larger data.
For example, you entered www.valuehosted.com in the address bar
Our server responded and opened a full-resourced website for you.
Sent website URL = Small data packets
Server opened the website = Large packets received at your end
The attackers infiltrate the DNS (Domain Name System) servers and NTP (Network Time Protocol); send requests to NTP via botnets and the requests expects a large response from the server. If the server is unable to respond with requested data, it will crash with seconds as there will be hundreds and thousands of incoming malicious requests.
In simple.
Attackers use botnets, amplify it on an online portal (called stressers, mostly available on the dark web) and first send a tiny (in bytes) to the target server.
Once the request penetrates the NTP, the network than realizes that the request contains a much large response.
For example, the attacker sent 1kb of malicious request
This request further request 200MB of response. Now do the math.
How much will the large malicious requests be requesting from the server?
The attacker sends 200GB from one botnet and requested 1T. What will happen? Your website, server, network everything will crash within seconds.
Amplified DDoS attacks are enough to even take down websites like Google, YouTube, Facebook, and many others.
DID YOU KNOW?
On 3rd January 2018 (Wednesday) at 12:15 pm EST, GitHub, a renowned developers’ platform, received an amplified DDoS attack of 1.35 TB per second (most powerful DDoS attack in the history). The attacks stayed from 8-10 mins until finally Akamai Technologies came forward and routed incoming and outgoing traffic from GitHub to block all the malicious packets.
Source: Wired

How many types of DDoS attacks are there?
The DDoS attacks revolve around the OSI Model (Open Systems Interconnection). There are 7 types of DDoS attacks that you should be well aware of if you’re in the IT industry.
- Layer 1 – Attacks the physical layer that is responsible for transferring primary (raw) data to the network’s hardware
- Layer 2 – Attacks the datalink layer that determines the format of data
- Layer 3 – Attacks the network layer to dismantle data routes. This layer assigns incoming data with routes to propagate. It crashes the network by occupying all the capacity so that no other data request, other than DDoS, is present.
- Layer 4 – Attacks the transport layer that contains the UDP, TCP transmission protocols
- Layer 5 – Attacks the session layer that manages the user sessions and data connections
- Layer 6 – Attacks presentation layer that performs data encryption and also handles the data formats
- Layer 7 – Attacks the application layer that acts as a medium layer between the user and web server (when we click to open web applications)
Value Hosted offers excellent DDoS protection of Layer 3,4 and 7 as these three are attackers’ favourite for shutting down network servers.
